Security Questionnaire Examples: Top 20 Questions & How to Respond

1up analyzed more than 10,000 real security questions from an anonymized and sanitized set of questionnaires. Here's what we learned.
Look, if you've ever opened your inbox to find a 200-row spreadsheet titled something like "Vendor_Security_Assessment_v3_FINAL_FINAL.xlsx", you already know the feeling. Stomach drop. Calendar wreckage. The dawning awareness that this is going to eat your whole week. We've been there. A lot.
The thing is, how you handle these questionnaires actually matters. A solid response builds data security trust with your prospect. A sloppy one makes them quietly start shopping for alternatives, even if your tech is better than the competition's.
And the stakes keep going up. One breach, one bad headline, and procurement teams across an entire industry get an email from their CISO that basically says "tighten the screws on every vendor we work with." That's roughly the climate we're in now. We've talked to security leaders who say the questionnaires they're sending out today are 3x longer than what they sent two years ago.
Here's the kicker. A scrappy 10-person Series A startup will sometimes get hit with the same questionnaire format as a Fortune 500. Same 200 questions. Same "respond by next Tuesday." Doesn't matter that you don't have a dedicated security team yet.
Anyway. We pulled the 20 questions that come up over and over across the questionnaires we've seen, plus the example answers we like. For each one we'll tell you what your buyer is fishing for, how to actually respond, and what a strong answer looks like. After that, five rules for writing answers that move deals along instead of just checking boxes for the auditor.
Prepping for a SOC 2 audit? This will help. Trying to clean up old policies before next quarter's enterprise push? Also helpful. We've also dropped a free security questionnaire response template you can grab if you want somewhere to start.
The 5 Most Common Categories of Security Questions
Pretty much everything you'll see breaks down into five buckets. There's overlap in places, and some questions live in two categories at once. But this is how we mentally sort the chaos.
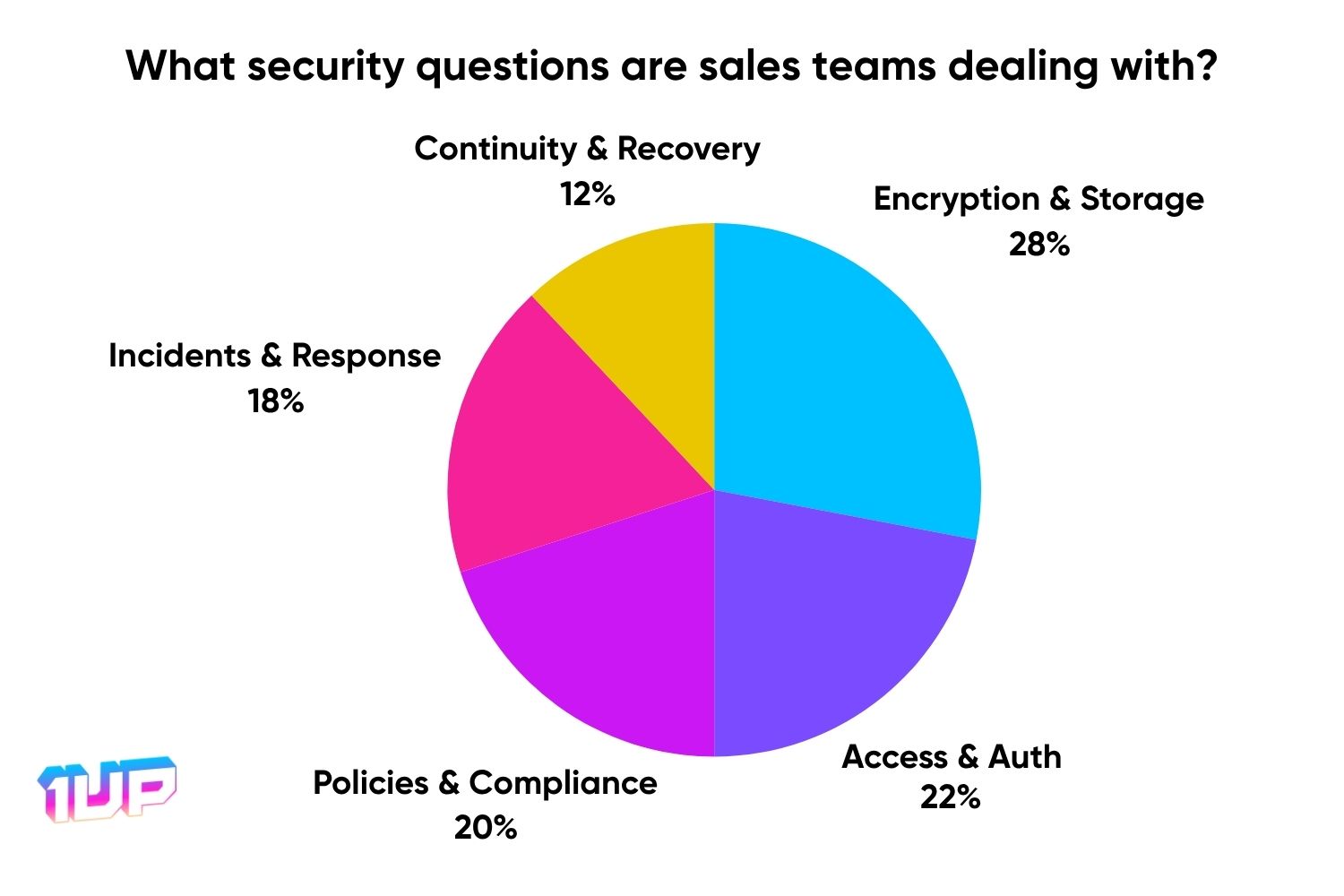
1. Data Protection and Encryption
This bucket is the data itself. Where it lives, how it gets around, what happens to it overnight when nobody is poking at it. Geography matters here a lot more than most companies realize until the day they have to answer for it. Backups too. The question your prospect is silently asking is: would your backups bail you out if today turned into the worst Wednesday of your year, or would they fail you in some quietly catastrophic way you haven't tested for.
Look out for questions on encryption at rest and in transit, where customer data is physically located, and how often you back things up.
2. Access Control and Authentication
Boils down to who can see what. Your prospect is trying to work out which of your employees can actually touch their data on a given Tuesday, how you decide that, and what hoops anyone has to jump through to get logged in. Good access control means that when (not if) one of your employees gets phished, the blast radius isn't existential.
Look out for RBAC questions, SSO and MFA setup, and how you handle admin or privileged accounts. Privileged accounts especially. Those tend to be where things go badly wrong.
3. Security Policies, Certifications, and Compliance
This one is mostly a maturity check. Has anyone written your security stuff down? Has someone outside the company actually looked at it and said, yeah, you're doing the things you say you're doing? And do your employees know any of this stuff, or did they sit through one PowerPoint on day one and then promptly forget it forever?
Questions in this bucket cover written policies, your standing on stuff like SOC 2, GDPR, HIPAA, and what your employee awareness training actually looks like in practice.
4. Incident Management and Vulnerability Response
Controls fail eventually. Even the great ones, on a long enough timeline. What matters more than the failure itself is what your team does in roughly the half hour after the failure. Do you call your customer? Do you actually dig into root cause, or do you slap a patch on top and move on? These are not abstract questions. Your prospect probably has a war story they don't want to repeat.
Look out for questions about breach notification timelines, your incident response playbook (assuming you have one), how often you scan for vulnerabilities, and how fast critical patches actually get deployed.
5. Business Continuity and Disaster Recovery
Bad stuff happens. Sometimes it's a botched deploy on a Friday afternoon, sometimes it's a full AWS region going dark for hours (which has happened more times than the cloud providers will fully admit on a status page), and once in a while it's some genuinely cursed combination of things going wrong all at once. We've all read those Hacker News postmortems.
Your prospect would just like to confirm that you've thought about this stuff before today, and that the plan is more substantial than "everyone gets in a Slack huddle and panics."
Look out for questions about your BCP/DR docs and how often you test them, your Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO), backup testing, and whether you have any alternate hosting sites.
The Top 20 Security Questionnaire Questions
Here's the long list. These are the 20 we see come up over and over, ordered roughly by how early they show up in a typical questionnaire (though every customer is a little different and some procurement teams just love throwing curveballs at you on question 4). For each one we've included what we think the buyer is actually fishing for, a way to answer, and an example you can rip and adapt.
1. Documented Information Security Policy
Question: Do you have a documented Information Security Policy reviewed and approved by management?
Why they're asking:
This one looks easy and isn't. A surprising number of companies fail it because either the policy genuinely doesn't exist, or it lives in some forgotten Notion page nobody has touched since 2023, or it does exist but nobody senior has signed it.

That last bit is what your prospect actually cares about. Anyone can write a security policy in a long weekend. Hard part is getting an executive to put their name on it and own it. Without exec ownership, security stuff gets quietly deprioritized the moment quarterly revenue numbers wobble. Procurement teams have learned this the hard way and now they ask up front.
How to respond:
Confirm the policy is real. Mention the exec who signed off (CTO, CISO, COO, whoever). Throw in your review cadence and how the team actually gets the doc.
Great example:
"Yes, we have a documented Information Security Policy that is reviewed and approved annually by executive leadership. Our policy is shared across the company, and it serves as the foundation for all of our security practices."
2. Third-Party Security Certifications
Question: What third-party security certifications does your organization maintain (e.g., ISO 27001, SOC 2 Type II)?
Why they're asking:
Sales decks tell whatever story is convenient. Auditors don't (mostly). That's why your prospect cares about certifications. A third party went through your work, kicked the tires, and signed something. The big ones in most questionnaires are ISO 27001 and SOC 2, and you'll start seeing newer privacy and AI frameworks pop up too.
Trying to land a Fortune 1000 deal without at least SOC 2 Type II is a path of pain. We have multiple customers who tried it. They got a lot of meetings, a lot of "we love you guys," and then somehow no contracts ever closed. Hmm.
.png)
How to respond:
List what you've got. Mention the auditor and the date. Say whether audits run annually or on a continuous basis.
Great example:
"We maintain SOC 2 Type II certification, which is audited by a third-party firm on an annual basis. We are also ISO 27001 certified, and our most recent recertification was completed in Q2 2025."
3. Encryption at Rest and in Transit
Question: How is customer data protected at rest and in transit (encryption methods, protocols used, e.g., AES-256, TLS 1.2)?
Why they're asking:
Encryption is one of the easy ones, which is why it's almost always near the front of a questionnaire. The prospect is mostly just confirming the obvious: that you aren't keeping plaintext customer data lying around on some old MySQL box, and you aren't yeeting it across the public internet without TLS.
The thing is, "obvious" is doing a lot of work in that sentence. We have honestly seen vendors fail this one. Not many. But it happens. And if your encryption story doesn't include AES-256 at rest plus TLS 1.2 or better in transit in 2026, the conversation tends to end shortly after.
.png)
How to respond:
Just name the protocols. AES-256 at rest. TLS 1.2 or better in transit. Toss in your key management approach if it's worth bragging about (something like AWS KMS, Google KMS, or a real HSM).
Great example:
"We keep our customer data encrypted at rest using AES-256 and in transit using TLS 1.2 or higher. Our encryption keys are managed using AWS KMS with strict access controls."
4. Backup and Recovery Process
Question: What is your backup and recovery process, including frequency, retention, and testing of backups?
Why they're asking:
Backups are your last line of defense after everything else has gone up in smoke. The drive dies. An overworked intern drops the users table. Some piece of ransomware encrypts your prod database while everyone is at lunch. Take your pick.
What your prospect actually cares about is not the existence of backups. They care whether you've ever actually pulled one back from the dead and restored it cleanly. There's a thing we see depressingly often where a company has had nightly backups for five years, never tested the restore even once, and only discovers on the day they need it that the restore script silently broke six months ago and nobody noticed because nobody was looking.
Restore tests are the whole game. Run them.
.png)
How to respond:
Hit the four things: how often you back up, how long you hold them, where they live, and how often you actually run the full restore end-to-end (not just spot-check that the file exists).
Great example:
"We perform full backups every night, and we retain records for 90 days. We also encrypt and store data in a separate region. We test our entire recovery process on a quarterly basis."
5. Business Continuity and Disaster Recovery
Question: Do you have a documented Business Continuity Plan and Disaster Recovery Plan? How often are these plans tested?
Why they're asking:
The question your prospect is really asking is something like: "If your office floods on a random Wednesday morning, or if your primary AWS region disappears for six hours, or if a contractor pushes a bad migration on a Friday at 4:55pm and goes home, what happens to my data?"
A doc by itself is the easy part. Anyone can write a 30-page BCP in an afternoon (we've literally seen ChatGPT spit one out). The thing that makes the plan real is testing it. Tabletops are good. Live drills are better. Actually shutting down a region in production and watching your team handle it is the gold standard, although it requires the kind of confidence most teams don't have. A BCP that's never been tested is closer to fan fiction than disaster planning.

How to respond:
Confirm the plan is real. Cover what scenarios it includes. Mention how often you test and what kind of testing (tabletop, live drill, a full simulation).
Great example:
"Yes. We maintain a Business Continuity and Disaster Recovery Plan that is reviewed and tested on an annual basis. We use both tabletop and live simulation exercises."
6. Access Management and RBAC
Question: How is access to systems and customer data managed and controlled (e.g., RBAC, least privilege, access reviews)?
Why they're asking:
The translation here is, how cluttered is your permissions situation, really. Like, if someone audited your IAM tomorrow, would they be horrified.
The answer involves least privilege (give people only what they need) plus RBAC (assign access via roles, not one-off favors handed out by a manager who got tired of waiting on IT). The bit that frequently undoes companies is the access review cadence. People rotate teams. Projects end mid-quarter. Someone quits on a Friday morning and is starting at a competitor that following Monday.
If nobody is reviewing access on some kind of cadence, the orphaned permissions just accumulate quietly in the corner. Then somebody, somewhere, uses a forgotten six-month-old admin token, and you have a "Slack channel on fire" kind of morning followed by a much worse afternoon.

How to respond:
Walk through your RBAC setup. Mention least privilege. Say how often you do reviews.
Great example:
"We manage access through role-based access control with least privilege enforced. We also review access on a quarterly basis and remediate any anomalies promptly."
7. SSO, SAML, and MFA Support
Question: Do you support Single Sign-On (SSO), SAML, or Multi-Factor Authentication (MFA) for secure authentication?
Why they're asking:
A huge chunk of breaches still start with a stolen password. The Verizon DBIR has been beating this drum every single year and somehow the lesson keeps not landing for everyone.
So your prospect wants two things at once. They want SSO and SAML so they can wire your product into whatever identity provider their org has standardized on (Okta in a lot of cases, Entra if they're heavy Microsoft, Google Workspace if they're a more modern shop). And they want MFA actually enforced, not just available, especially for accounts that could blow things up.
Missing either one of those in 2026 is mostly a non-starter for any kind of serious enterprise sale. Honestly, the deal won't even get out of the procurement stage.
How to respond:
List the auth methods you support and how MFA is enforced.
Great example:
"Yes. We support SAML-based SSO and enforce MFA for all internal and administrative users."
8. User Account Provisioning
Question: How do you provision and de-provision user accounts? Are regular access reviews conducted?
Why they're asking:
True story. Friend of ours left a Series B startup, and three months later he could still log into their production AWS console. Just out of curiosity. He flagged it to the team. They thanked him politely. He wasn't even on their security team. He was a frontend engineer.
This kind of thing is genuinely everywhere. Your prospect knows it. They want to see your provisioning runs off your HR system (Workday, Rippling, BambooHR, whichever) and that the moment someone resigns or gets walked out, their access disappears. Not "we'll do it in the next sprint." Not "by end of week." Hours, ideally. Same day at worst.

How to respond:
Describe your onboarding and offboarding flow. Say how often you review access.
Great example:
"All of our accounts are provisioned through HR-driven workflows. Deprovisioning takes place in our facility within 24 hours of termination of employment or contract. We also conduct access reviews monthly."
9. Background Checks and NDAs
Question: Do you require background checks and confidentiality agreements for all employees and contractors?
Why they're asking:
The huge majority of insider threats are extremely boring. Sloppy practices. A frustrated employee being careless because they're already half checked out. A contractor who doesn't really care because they're rolling off in a month. Movie-villain insider threats basically don't exist outside Hollywood.
The basics still matter though. Run a real background check before someone gets near customer data. Have everyone sign an NDA before day one. Your prospect just needs to confirm you aren't handing prod credentials to whoever responded to your Craigslist ad last Tuesday afternoon.

How to respond:
Be specific. What screening, when, and what does everyone sign before getting access?
Great example:
"Yes. All employees and contractors undergo background checks and sign NDAs before they access any systems or are privy to customer data."
10. Security Training Programs
Question: What security training programs and awareness measures are in place for employees?
Why they're asking:
Phishing keeps working. Always has, probably always will, because phishing emails keep getting noticeably better and people are tired and busy. Even smart, careful people click on stuff sometimes. We've all almost done it.
What your prospect wants to see is that you're at least trying. Once-a-year compliance training is mostly performative at this point. Most decent programs run quarterly or monthly phishing simulations, plus some kind of ongoing nudge. The other thing, which honestly matters as much as the training itself, is whether your culture punishes people for clicking on stuff. Because if it does, nobody reports anything, and your detection time goes way up.
How to respond:
Tell them how often you train, what topics you cover, and whether you do anything beyond videos like phishing simulations.
Great example:
"Security training is mandatory during onboarding and conducted once a year after that. We also run phishing simulations every quarter."
11. Incident Detection and Reporting
Question: How do you detect, respond to, and report security incidents and data breaches, including notification procedures and timelines?
Why they're asking:
This is the breach question. It tends to get the most scrutiny from your prospect's legal team, especially if their data is regulated.
What they're looking for is detection that's at least reasonably fast, a real working playbook (not a pretty flowchart someone drew up just to put in a deck), and customer notification within whatever the legal window is. GDPR is 72 hours. Several US state laws are tighter than that. Some industries (healthcare, financial services) are tighter still. Vague answers about "we have processes in place" sink credibility instantly. The reviewer has read 60 of these. They know what real looks like.

How to respond:
Detection tools. Response process. Notification timeline. Be precise on the time, since they'll compare you against the law.
Great example:
"We use a SIEM for real-time threat detection. We triage any incidents within one hour, and if customers are impacted, we report to our customers within 72 hours, which is required by law."
12. Vulnerability Scans and Pen Tests
Question: Do you conduct regular vulnerability scans and penetration testing? What is your process for remediating identified issues?
Why they're asking:
Software has bugs. Infrastructure has misconfigurations. There is a more or less 100% chance that there is something exploitable in your stack right now, somewhere, that you don't know about. Probably more than one thing. Sorry to break that news.
The interesting question your prospect is actually probing on: who finds the issue first? Your team via scanning? An outside security researcher who happens to look? An attacker?
Continuous automated scanning catches the dumb stuff fast. An annual pen test from a real outside firm catches the cleverer stuff that scanners miss. And then the third part, which a lot of companies forget about, is what happens after a finding gets opened. A critical-rated bug that quietly rots in a Jira backlog for nine months might as well not have been found at all.

How to respond:
Share your scan cadence, your pen test schedule, and your SLAs for fixing what gets found.
Great example:
"We run weekly automated vulnerability scans on all of our assets. We also perform external penetration testing annually, and we resolve critical issues within 7 days."
13. Audit Trails and Logging
Question: Is there an audit trail or logging of access and changes to customer data? How is this data protected and retained?
Why they're asking:
Logs are how you figure out what really happened after something goes sideways. They're also how your prospect would figure out what happened to their data, if they ever needed to do that kind of forensic work.
There's a catch though. Logs are only useful if an attacker who's already inside your environment can't quietly edit them. Otherwise they're worse than nothing because they give a false sense of security. So storage matters. Tamper-evidence matters. Retention matters as well, and a lot of frameworks want a minimum of 12 months of logs available. PCI is famously picky about all of this.

How to respond:
Mention what you log, how long you keep logs, and how they're protected from tampering.
Great example:
"We log all access and modifications to customer data. We also encrypt and retain everything for 12 months. We then review our logs during every quarterly audit."
14. Monitoring for Suspicious Activity
Question: What controls are in place to monitor for unauthorized or suspicious activity (e.g., SIEM, IDS/IPS)?
Why they're asking:
This is the always-on version of detection. The prospect wants to feel confident that something or someone is paying attention when stuff goes weird at 3am Pacific on a long weekend.
SIEMs do most of the heavy lifting on aggregating events. IDS and IPS pick up the network-level weirdness. But the question the prospect is sort of asking sideways here is whether anyone would respond to an alert at 3am Pacific on a long weekend, or whether the alert would sit in a queue until someone noticed it on Monday at the 10am standup. The gap between detection and response is where almost all of the actual damage happens.

How to respond:
Describe the tools running and who's watching them.
Great example:
"We use a managed SIEM solution with built-in IDS. Our 24/7 security team triages all alerts, and they escalate based on our predefined security levels."
15. Physical Security Controls
Question: How do you ensure physical security for systems and media storing or processing customer data?
Why they're asking:
If your company is a fully cloud-hosted SaaS, this one feels a little 2014. It still shows up in questionnaires though, because the questionnaire template was probably written in 2014 and just never properly refreshed.
If you're on AWS, GCP, or Azure, the answer is roughly: we inherit the physical controls from our cloud provider, who is themselves SOC 2 and ISO 27001 certified. Point at their compliance docs and call it. If you have any on-prem hardware (some companies still do, especially in regulated industries like healthcare and certain corners of finance), you'll need to talk about your own physical controls. Cameras, badge access, escort policies for visitors, the whole package.

How to respond:
Name your hosting environment, the certifications it carries, and the physical access controls. Inherit from the cloud provider where you can.
Great example:
"Our infrastructure is hosted on AWS, which is ISO 27001 and SOC 2 certified. Our data centers have biometric access and video surveillance. We also have staffed security."
16. Data Residency Controls
Question: Are customer data and backups only stored in agreed-upon geographic locations? Can customers select their data residency region?
Why they're asking:
GDPR really opened this whole thing up back in 2018, and now there are similar data residency laws in dozens of jurisdictions. Some prospects literally cannot, legally, let their data sit outside a specific region. EU buyers want EU residency at a minimum. German buyers sometimes want Germany-only. Indian regulators have gotten a lot more assertive about this lately.
So the question becomes: can the customer pick a region, and will you honor it everywhere? Including for backups, log files, error monitoring, and any analytics processing you do behind the scenes. Honoring residency for the primary database but quietly shipping all your logs to us-east-1 is the kind of thing that sinks a renewal once a sharp compliance person finally clocks it.

How to respond:
Explain the default. Mention region selection if you offer it, and confirm backups stay in the same region as the primary data.
Great example:
"We store customer data and backups in the selected region. Our customers can specify their preferred data residency region during the onboarding process."
17. Data Retention and Destruction
Question: What is your data retention and secure destruction policy for customer data and media?
Why they're asking:
Data you don't need anymore is basically liability sitting on a balance sheet that you don't see in any quarterly report. The longer something hangs around, the more chances something bad happens to it that you really, really would not want to explain to a regulator on a Wednesday morning.
Two pieces to think about here. First, do you actually purge customer data after a contract ends, or does it just keep sitting in your warehouse forever because nobody owns the cleanup. Second, when you do "delete" something, is it actually gone? A row dropped from a Postgres table is technically recoverable until that storage block gets overwritten by something else. NIST 800-88 spells out how to actually destroy data for real, including the awkward cases like SSDs and tape archives (yes, some companies still archive to tape, no really).

How to respond:
Cover the retention window, the deletion mechanism, and any standards you follow for the destruction process (NIST 800-88 is the one to cite).
Great example:
"We retain customer data for 30 days after a contract has been terminated unless otherwise requested. We securely delete data using NIST 800-88 compliant methods."
18. Environment Separation
Question: Are your development, testing, and production environments separated? How is production data controlled in non-production environments?
Why they're asking:
Plenty of companies have prod, staging, and dev sharing way too much infrastructure for comfort. Some copy production data straight into test environments because building good synthetic data is genuinely a pain in the neck. We've seen it. We've done it ourselves earlier in our careers and would absolutely not recommend.
Your prospect knows this shortcut is super common and they really, really don't like it. They want confirmation that your environments are properly walled off, and that real customer data isn't ending up in some test database where a junior dev can prod at it from their personal laptop on a coffee shop wifi network.

How to respond:
Talk about how the environments are isolated and what you do for masking when test data is needed.
Great example:
"Yes. We keep our environments fully separated. We never use production data in test environments, and we anonymize all test data using irreversible masking techniques."
19. Data Loss Prevention
Question: Do you have DLP (Data Loss Prevention) controls to prevent unauthorized data transfer or leakage?
Why they're asking:
DLP is roughly the thing that prevents Bob in accounting from forwarding the customer list to his personal Gmail at 8pm on a Sunday because he just wanted to work from the couch and was tired of VPN-ing in. Most data leaks look like this. Accidental, dumb, no malicious intent at all. The damage to your company is exactly the same regardless.
The prospect wants to confirm you've got actual DLP that actually does things, not a policy document somewhere that says "please do not exfiltrate sensitive data" which nobody has ever read or signed.

How to respond:
Name the DLP products and where they sit (endpoint, email gateway, browser, etc.). Mention how the rules get updated.
Great example:
"We use endpoint and email-based DLP tools to detect and block unauthorized sharing of sensitive information. We regularly review and update all of our rules."
20. Ongoing Legal Compliance
Question: How do you ensure ongoing compliance with relevant data protection laws (e.g., GDPR, HIPAA, PCI)?
Why they're asking:
GDPR. HIPAA. PCI. CCPA. The EU AI Act. Whatever weird new state law got signed last month while you were on vacation. Compliance is a constantly moving target, and approximately fourteen more frameworks are coming down the pipeline that nobody has even started thinking about yet.
What your prospect wants to understand is how you keep up. Specifically: is there an actual person whose job this is, or is it kind of distributed across a few people which usually translates to nobody really owning it? Are you running real internal audits, and how often? Are the controls themselves implemented in production, or are they written down somewhere as aspirations and quietly ignored?
.png)
How to respond:
List the regulations you follow and how you track changes plus prove compliance.
Great example:
"We maintain a compliance register for GDPR, HIPAA, and PCI DSS. We conduct internal quarterly audits, and we have external legal counsel review material changes."
How to Respond to Security Questionnaires (5 Rules)
Why am I getting 200 questions about my security posture?
If you've spent any real time in Sales or IT, you've probably filled out a compliance questionnaire at some point. But if this is your first one, and you're staring down a wall of requirements with a deadline attached, the question on your mind is probably: what did I do to deserve this?
Don't stress. You're not alone in the slightest.
Knowledge workers everywhere are dealing with the same pain right now. These questionnaires come from customers, partners, investors, and suppliers. Their vendor risk management process forces them to vet any third party they work with, and you happen to be a third party.
Yeah, these things are painful. They're distracting. They're often confusing on top of everything else.
We get it. Most people just want to get them over with. The catch is that a strong response can genuinely make or break a deal.
Here are five rules for writing a response that doesn't suck.
Rule 1: Keep It Simple
Third-party risk questions are already loaded with jargon. Adding more on top, in your response, doesn't help.
Long, padded answers slow the reviewer down. That's bad for them and bad for you. Short, direct answers move the questionnaire (and the deal) along faster.
For example, if you're asked, "Describe which security certifications your product meets":
A good answer looks like this:
"We meet PCI-DSS, GDPR, and SOC2 Type 2 compliance."
A bad answer drags on without getting to the point:
"We meet a variety of compliance certifications that extend above and beyond the norm. These certifications demonstrate our commitment to information security standards. We meticulously adhere to the highest standards of compliance, ensuring that our operations, systems, and processes align flawlessly with the stringent requirements of PCI-DSS, GDPR, and SOC2 Type 2."
Nobody wants to read that. Keep your responses direct and to the point. Your reviewer will thank you, and you'll improve your odds of winning the deal.
Rule 2: Provide References and Links to Documentation
Linking out is one of the easiest ways to build credibility in a questionnaire response.
The questions cover a huge range. Product architecture, employee training, encryption, retention. Most of your answers will point to some internal policy or doc anyway.
Add a link or reference where you can. It saves the reviewer the inevitable follow-up email asking for proof.
Here's a simple formula for a great response:
- Answer the question or requirement in under 100 words
- Add comments or an explanation if needed
- Include links to documents, URLs, diagrams, policies, and visuals
Web links, architecture diagrams, and pointers to company docs make your responses feel real instead of marketing fluff. A central questionnaire knowledge base keeps the docs together so your team isn't hunting for the same files every time a new questionnaire shows up.
Need help? Download our free Security Questionnaire Response Template:

Rule 3: Be Honest About Everything
Vendor risk management runs on transparency. Security questionnaires are not RFPs, where sales teams sometimes get a little creative with what's possible.
On the security side, you need to be straight. Be clear about how you meet each requirement. If you don't meet one, say so. Sometimes you'll fall short, and that's actually fine.
Stop assuming you have to say "YES" to everything to win the deal. You don't.
If you don't meet a requirement, explain why and how you make up for it.
For example:
Question: Do you require a minimum of 16 character complex passwords?
Answer: No, we require a minimum length of 8 character passwords. However, we also mandate Multi-Factor Authentication (MFA) for all users.
A flat "No" makes you look worse than you actually are. Always take the chance to explain why and reframe so your product comes across in a stronger light.
Rule 4: Automate the Questionnaire Workflow
Staring at a risk management questionnaire for hours feels like a colossal waste of human time, because it kind of is.
The same questions show up over and over. What kills people is doing the same manual search, research, and rewriting cycle every single time.
Even copy-paste is a slog, because you have to rewrite each pasted answer to match the new wording.
We did a study and found that a 2-person team can spend up to 12 hours on a single 100-question response. A central response database cuts that down a lot by giving the whole team approved answers they can pull from. Here’s what questionnaire automation looks like with 1up:
Pulling fast answers from accurate data is a massive time-saver on its own. Beyond just generating answers, decent automation handles the full workflow, like:
- Auto-explaining answers and showing sources
- Updating responses for the next time
- Tracking questionnaire progress
- Assigning teammates to review
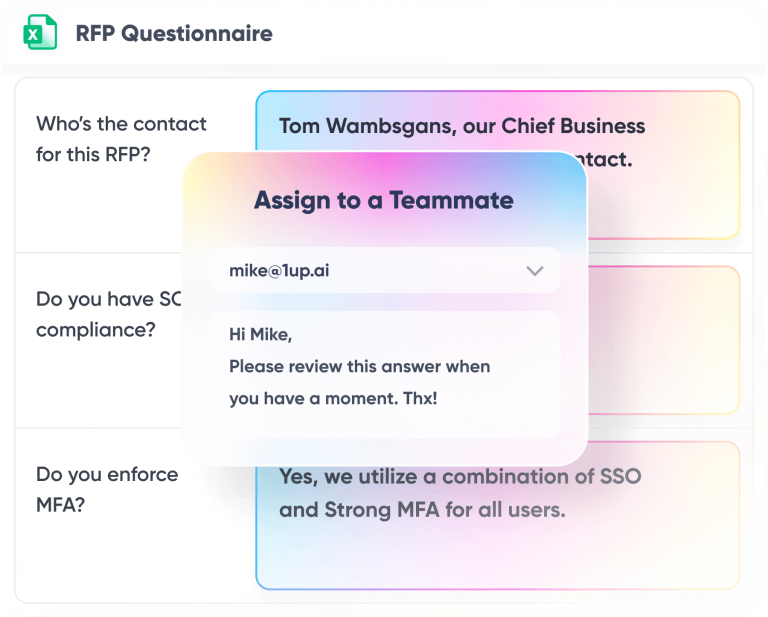
That's the busywork that should never have been on a salesperson or a security engineer's plate in the first place.
Rule 5: Address Gaps and Potential Objections
Use the response to handle objections before they actually come up. Every question is a chance to get out ahead of pushback that's coming anyway.
If you have to answer "No" or "Non-compliant":
Ask the customer why the requirement matters to them in the first place. Then offer alternatives or similar things you do well.
If it's on the roadmap, say so:
Sometimes you just have to sell the roadmap. Customers actually appreciate it when you share where the product is going. Just don't promise stuff that's a year out or anything you can't actually show.
Throw in proof points:
Mention customers, real deployments, success stories where they fit naturally.
Set traps for the competition:
If you're in a competitive deal, this is your shot to make their life harder. Drop in questions or comments that your buyer could turn around and ask the other vendor. Every answer is a chance to plant a doubt about whoever else is in the bake-off.
How to Get Better at Security Questionnaire Responses
The bar isn't perfection. The bar is professionalism, which is a much lower bar than people think.
Most of getting there is just preparation work done ahead of time. Document your controls. Make sure the people on your team know the story well enough to riff on it during a sales call without freezing. Build a centralized knowledge base of approved answers so you aren't rewriting the same paragraph from scratch for the fourteenth time this quarter. The whole point is to not be the company scrambling at 11pm on a Thursday because procurement dropped 200 questions on you and wants them back Monday morning.
A confident, prepared response says you take security seriously. A scrambled, half-finished one says the opposite, even when your actual security posture is fine.
Anyway, most folks just hate doing these. They're long. They're repetitive. They pull your engineers away from product work that actually moves revenue. We see this constantly across the customers we work with.
Which is where we come in. 1up automates security questionnaire responses by pulling all of your security knowledge into one place and generating answers in whatever format your customer hands you, without your team having to do the same work over and over.
FAQs
Be transparent about what's missing, but make sure you outline your roadmap. For example: "We're currently implementing MFA and will have a full rollout completed by Q3."
Not every business has to have them, but they do streamline enterprise deals because they demonstrate external validation.
You should review your responses quarterly or after any major change to your infrastructure, policy, or staffing. Your security posture, of course, is not static.
Typically, a combination of the security lead, IT, compliance, and legal teams will be the responsible parties. You can designate one owner to coordinate an automated and collaborative questionnaire response.
Padding answers with vague corporate language. Reviewers want clear, specific responses. Long answers full of marketing speak slow them down and hurt your credibility.
1up your sales team